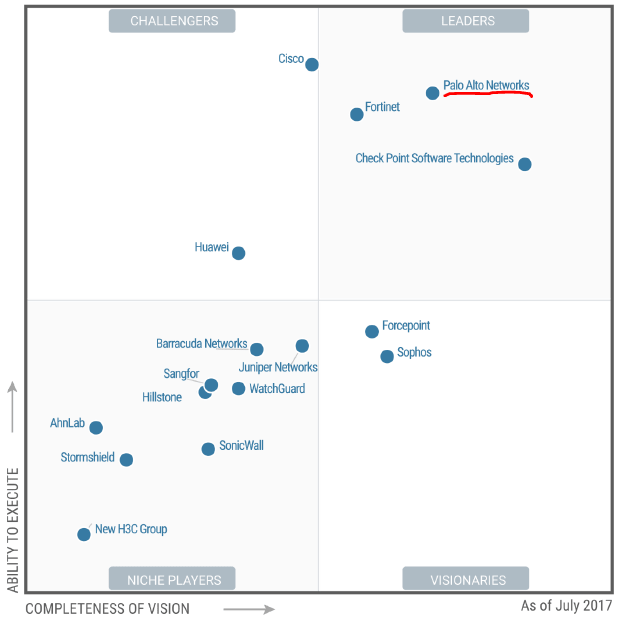
#1 Magic Quadrant for Enterprise Network Firewalls
“Next generation” capabilities have been achieved by all products in the enterprise network firewall market, and vendors differentiate on feature strengths.
Security and risk management leaders must consider the trade-offs between best-of-breed enterprise network firewall functions and cost.